IoT Botnet Forensics: A Comprehensive Digital Forensic Case Study on Mirai Botnet Servers - ScienceDirect
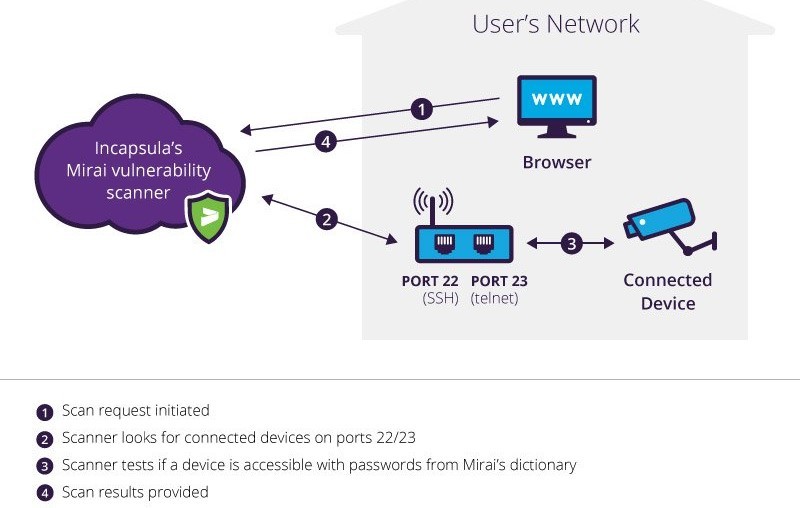
Sensors | Free Full-Text | A Malware Distribution Simulator for the Verification of Network Threat Prevention Tools | HTML

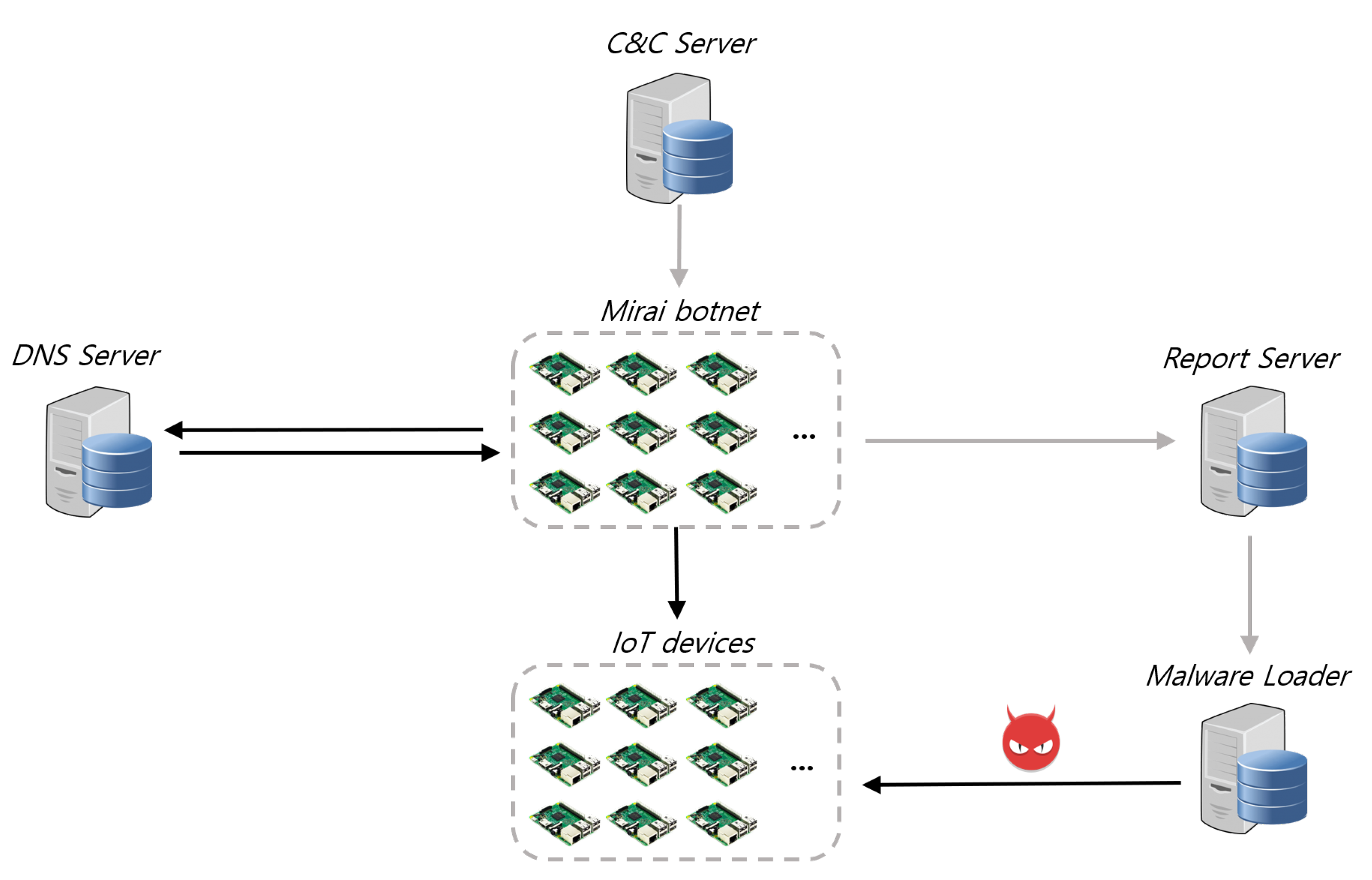
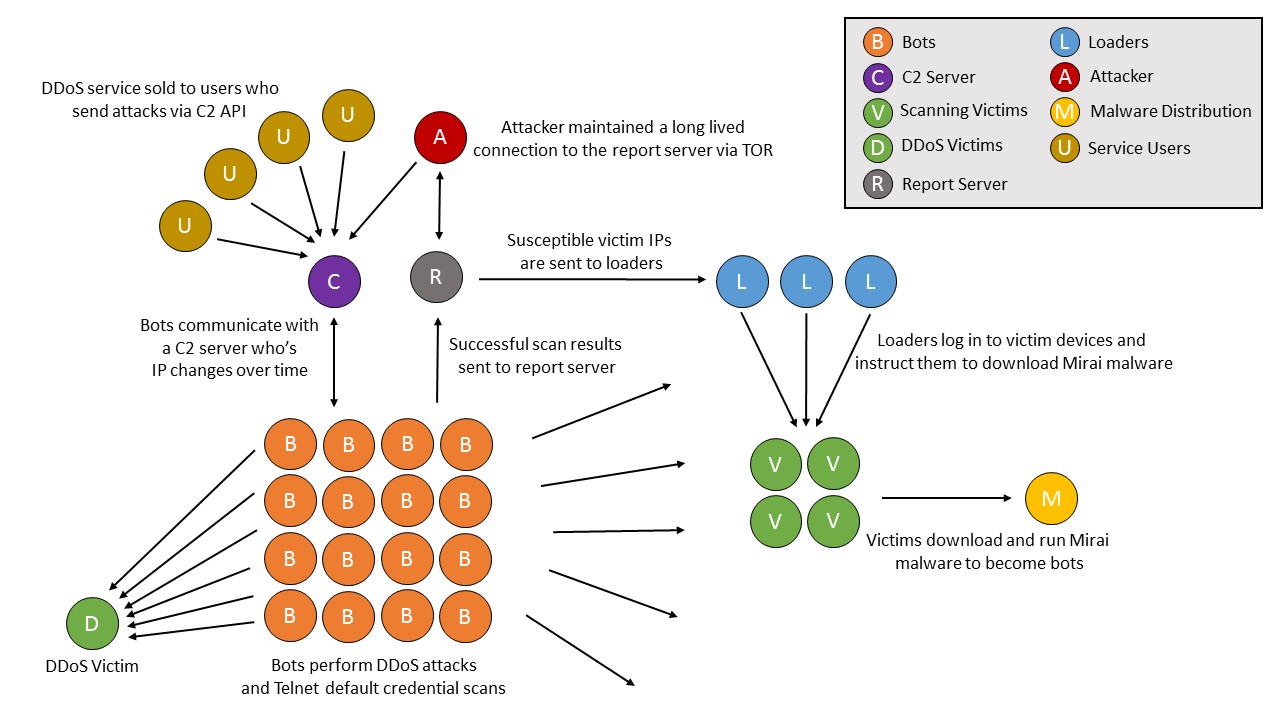
The Mirai Botnet Malware DDoS workflow, adapted from Level 3 Threat... | Download Scientific Diagram

Mirai botnet operation and communication. Mirai causes a distributed... | Download Scientific Diagram
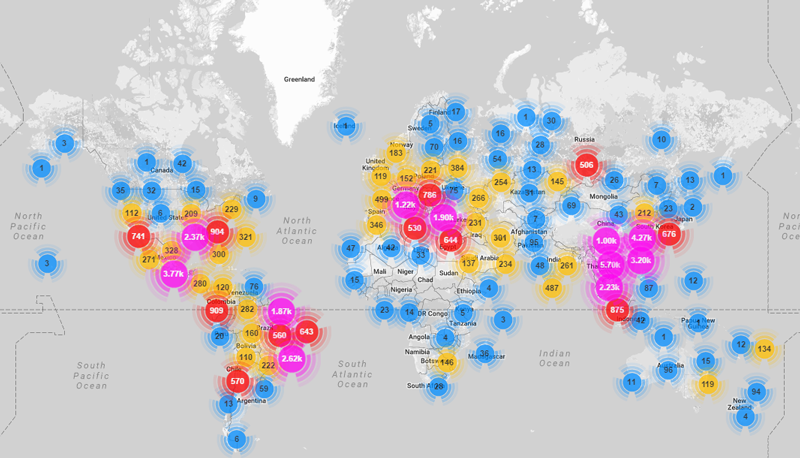
![PDF] N-BaIoT—Network-Based Detection of IoT Botnet Attacks Using Deep Autoencoders | Semantic Scholar PDF] N-BaIoT—Network-Based Detection of IoT Botnet Attacks Using Deep Autoencoders | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/6b8aec2a36d28f32b85163c7b1107767405d678a/6-Figure1-1.png)






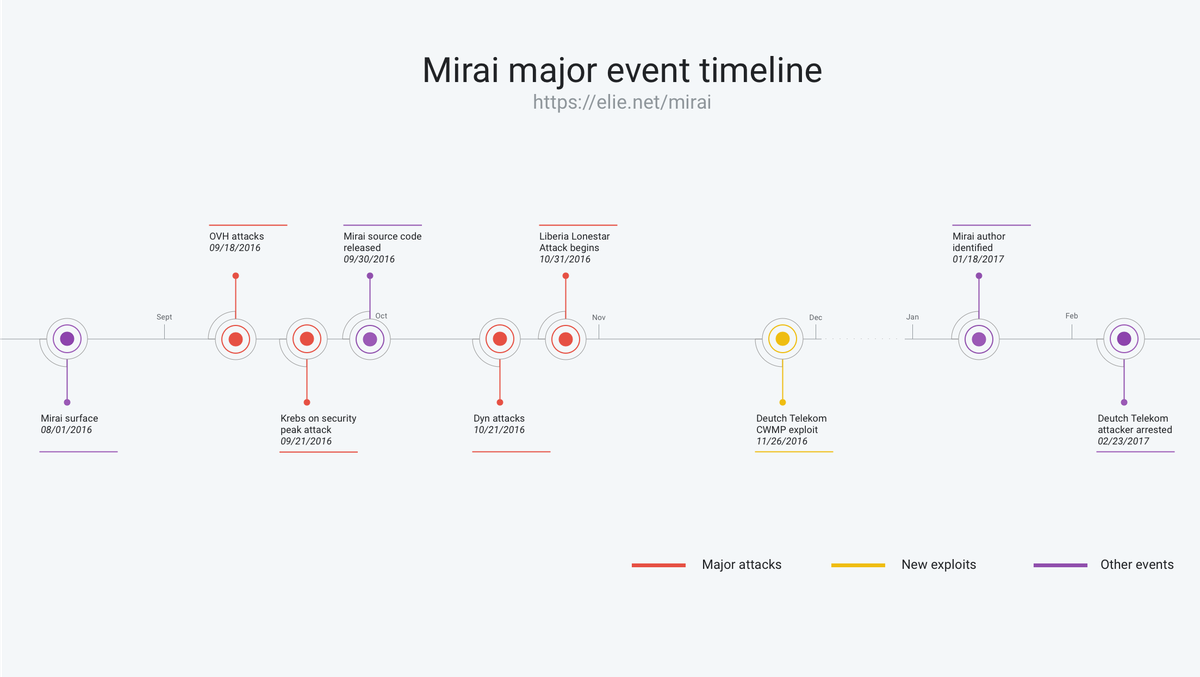
![PDF] The Mirai botnet and the IoT Zombie Armies | Semantic Scholar PDF] The Mirai botnet and the IoT Zombie Armies | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/271987d7dfb6456ae33ac8e2d8d576d4b5ee47d1/3-Figure1-1.png)